
Tailor the platform and its automated processes to align with your company's specific requirements and established policies.
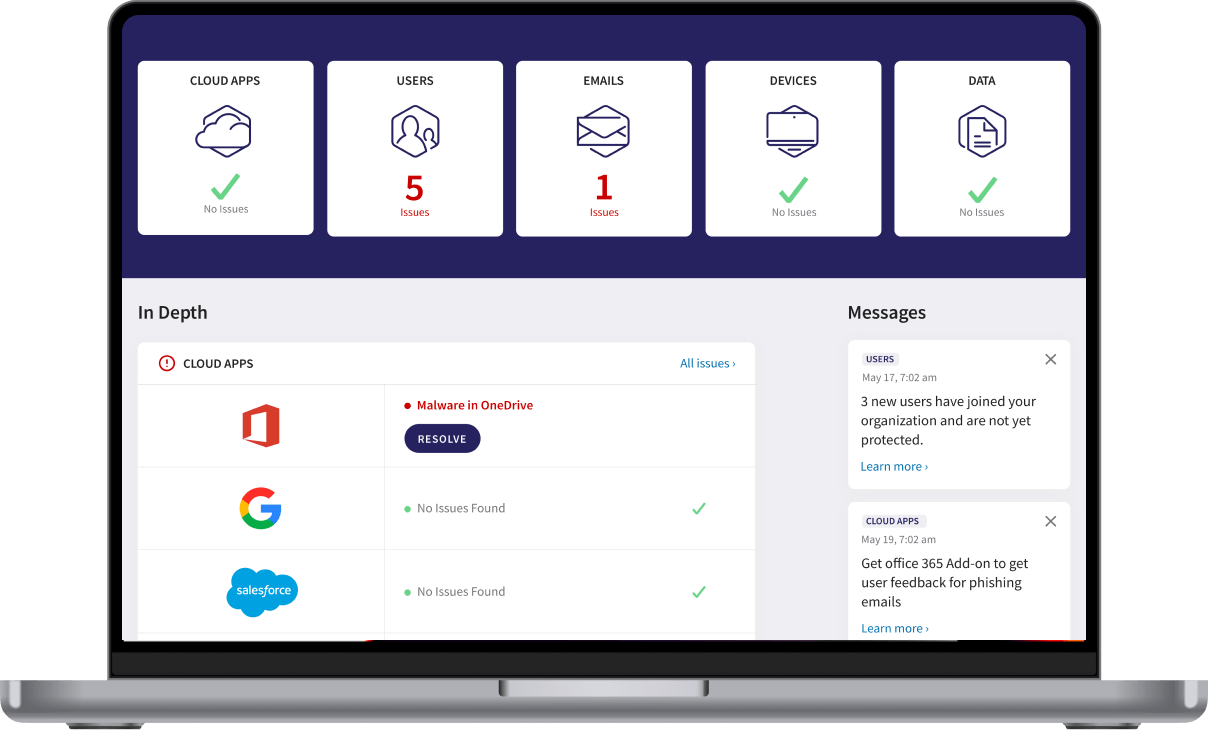
With GetCoro, your systems are under constant surveillance every day of the year, promptly identifying and addressing any potential threats.
The platform conducts continual scans for malware across all your devices, cloud applications, and email accounts, swiftly initiating remedial actions when necessary.
It automatically examines files and emails on all devices to detect regulatory data like Personally Identifiable Information (PII), Payment Card Industry (PCI), or Protected Health Information (PHI), promptly alerting you to any potential breaches.
By recognizing unusual login activities and thwarting hacking attempts automatically, GetCoro safeguards against both external malicious actors and internal threats.
Any identified threats are promptly isolated and reported to you, affording you the opportunity for manual investigation if desired.
GetCoro serves as the central hub for managing sensitive data and user activity, empowering you to uphold various security, regulatory, and organizational protocols effectively.


Employing AI-driven methods, GetCoro accurately distinguishes between human and bot-generated actions, allowing for the detection and mitigation of potential threats such as attacks or data corruption. Suspicious users can be promptly suspended to halt further file compromise.
Implement granular control over file, folder, and user sharing through collaboration rules, which allocate specific permissions and maintain whitelists of external collaborators.

Cyber defense strategies for the automotive sector involve measures to protect vehicles, manufacturing processes, and connected systems from cyber threats. They are crucial to safeguarding data integrity, ensuring vehicle safety, and maintaining operational continuity.
Embark on your journey towards enhanced cybersecurity solutions with the guidance and support of our experienced team.
Let’s Talk